Businesses have become increasingly aware of the need to support remote work, however, our inability to deploy remote working at the levels necessitated by the current global situation has shined a very strong light on organizational gaps in remote working programs and infrastructure.
Increased cyber attacks during this time have also made it clear how important it is for private sector businesses to pay very close attention to the security of their remote work solution.
How businesses have historically approached remote work
Businesses have a very wide range of remote work policies depending upon an organization’s focus on security and the level of institutional requirements it is subject to.
Historically, we’ve seen a range from “little to zero concern with the security of working remotely” for organizations in less regulated industries, all the way up to “top secret level protections” for organizations that contract with the government.
As such, the architectures employed for remote work have varied widely as well.
On the most secure end of the spectrum, you’ll see organizations that require employees to use employer-furnished devices to connect remotely.
In this case, the amount of remote work that can be supported relies 100% on the organization's ability to supply employer-furnished devices (laptops, smartphones, tablets, etc.) to staff.
In general, the costs associated with having enough employer-furnished devices ready for the entirety of an organization's staff, regardless of whether they might typically work remotely, are not usually feasible.
More specifically, in this case, where remote working needed to be ramped up very quickly, and with little involvement from centralized IT support teams, this approach is not only impractical but completely impossible.
Somewhere in the middle of the spectrum, we see companies that allow connection to the corporate network from personal devices with the use of some kind of VPN for security.
And in a significant number of cases, we see businesses that rely more heavily on cloud-based technology for collaboration and storage so as to have no “internal network” at all.
🔎 Related Articles: Future Proofing Remote Work for the US Government
Combining VDI & VPN
If your organization is looking to implement a company-wide secure solution for remote workers that is not overly expensive, difficult to manage or maintain, and simple for employees, a combination of VDI and a hardware VPN may be the right fit.
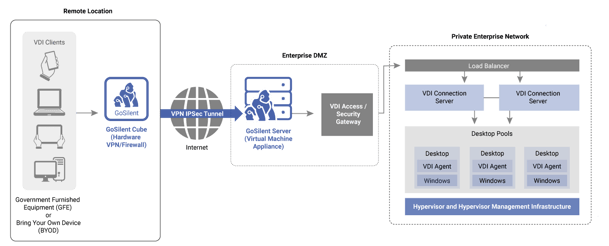
Combining Virtual Desktop Infrastructure (VDI) with a secure hardware VPN would allow your employees to securely connect to your corporate network from their own devices.
A VDI allows employees to work remotely through a virtualized environment that lives on your central server. Remote employees’ devices connect via the VDI to virtual machines that you have set up on your server, allowing users to execute work as if they are on your internal network.
With VDI, no data is stored on the employee device. Instead, the user can simply see what is on the screen of the virtual machine and interact with it, but not store data from it. VDI supports a range of remote work technology, from laptops and desktops to tablets or mobile devices.
Combining this environment with a secure hardware VPN, like Archon's GoSilent Platform, protects all traffic and information flowing across the connection between the employee device and the central network. GoSilent has been certified for use even on government level data, meaning you get the most stringent levels of protection.
How it works
Setting up a virtualized environment using VDI is relatively quick and painless. All you have to do is go through the following steps to get your environment ready for high-volume access:
-
Build a “Golden” virtual desktop image that has the operating system set up and locked down the way you’d prefer, and install any components or software that your remote employees might need to execute their jobs.
-
From that golden image, build whatever number of individual virtual desktop instances (machines) you need in order to have one for each of your employees/end users. Setting this up on the order of 10,000 machines can be accomplished in a matter of hours.
To ensure that users are accessing their virtual machines securely and that no data can be compromised or accessed through eavesdropping, you’ll need a hardware VPN that ensures all virtual desktop traffic is delivered over a secure, encrypted channel.
Deploying a VPN in a bring your own device (BYOD) environment requires a device-, operating system-, and software-agnostic solution. In this case, a hardware-based VPN solution is far more attractive than a software-based VPN due to its ability to provide the required level of security regardless of your level of control over the types/ages of devices, frequency of updates, and software versions across all of your users’ personal devices.
Outfitting your network and users for secure access can also be accomplished much more efficiently and easily with a hardware-based VPN compared to a software solution.
As an example, doing this with Archon’s GoSilent involves the following steps:
-
Set up the server-side VPN components on your internal network to allow for VPN connection. This can be set up and completed in as little as 10 minutes.
-
Provide each of your users with a GoSilent Cube that allows their personal devices (ex. laptops, desktops, smartphones and/or tablets) to connect securely over the open internet to your internal network. (In today’s COVID-19 environment, it is very easy to ship these small devices directly to users).
-
Users connect GoSilent Cube to their devices (with no setup required for a simple, plug-and-play solution that even non-technical users can deploy in minutes), download your company’s desired VDI application, log in, and go!
Benefits of combining a VDI & hardware VPN solution
The primary benefits of executing a solution like this are:
-
Makes BYOD secure: Prior to this, Bring Your Own Device (BYOD) may have been allowed for your organization but would have posed significant security concerns. An architecture that combines VDI with a hardware VPN allows for the use of personal devices with no risk to your data.
-
Faster to implement: Getting a solution like this up and running can happen very quickly and with little involved effort by your centralized IT support team.
-
Better technical investments: The combined VDI and VPN solution will be less expensive overall than providing laptops for every employee. Reusing server space and device-agnostic VPNs is much easier, as each has far more applications than reusing a laptop.
-
No risk to your data: Because no data is ever stored on an end-user device, and all of the changes or modifications to your data is happening physically on your servers (inside your network, inside your data center facility), it is actually more secure than providing employer-issued devices, which can be lost or stolen, to your end-users.
-
Significantly lower management and maintenance: Managing the updates, patches, and setup of a combined VDI and VPN solution is next to nothing.
-
Allows users to mask connection endpoints: If you have employees who regularly travel around the world, sometimes it might be beneficial to your organization that potential bad actors do not know where users are connecting from or that they are connecting to your business network. Some hardware VPNs, such as Archon's GoSilent Cube, offer IP obfuscation to ensure users can connect securely to the internet, even in untrusted regions.
The future of remote work
As the COVID-19 pandemic has made clear, we need to be better prepared for situations that would require entire companies to work remotely with very little advanced warning. Achieving this will require significant and lasting change that will force organizations to have better plans in place for remote work.
Because a combined VDI and VPN solution is quick to deploy, easy to scale up and down as needed, and is actually more secure than most current methods in place, it is perfectly poised to change the way organizations approach remote work.
